Code
The Cyber Security Learning Environment (CSLE); CSLE is a framework for evaluating and developing reinforcement learning agents for control problems in cyber security. Everything from network emulation, to simulation, and learning in CSLE have been co-designed to provide an environment where it is possible to train and evaluate reinforcement learning agents for practical cyber security tasks. Code repository; Documentation 
awesome-rl-for-cybersecurity; A curated list of resources dedicated to reinforcement learning applied to cyber security. Code repository
gym-optimal-intrusion-response; gym-optimal-intrusion-response is a reinforcement learning environment for simulating attack and defense operations in an optimal stoppping game. Code repository
gym-idsgame; gym-idsgame is a reinforcement learning environment for simulating attack and defense operations in an abstract network intrusion Markov game. Code repository
Hopsworks; Hopsworks is a platform for horizontally scalable deep learning pipelines on top of Hadoop. Code repository; Blog 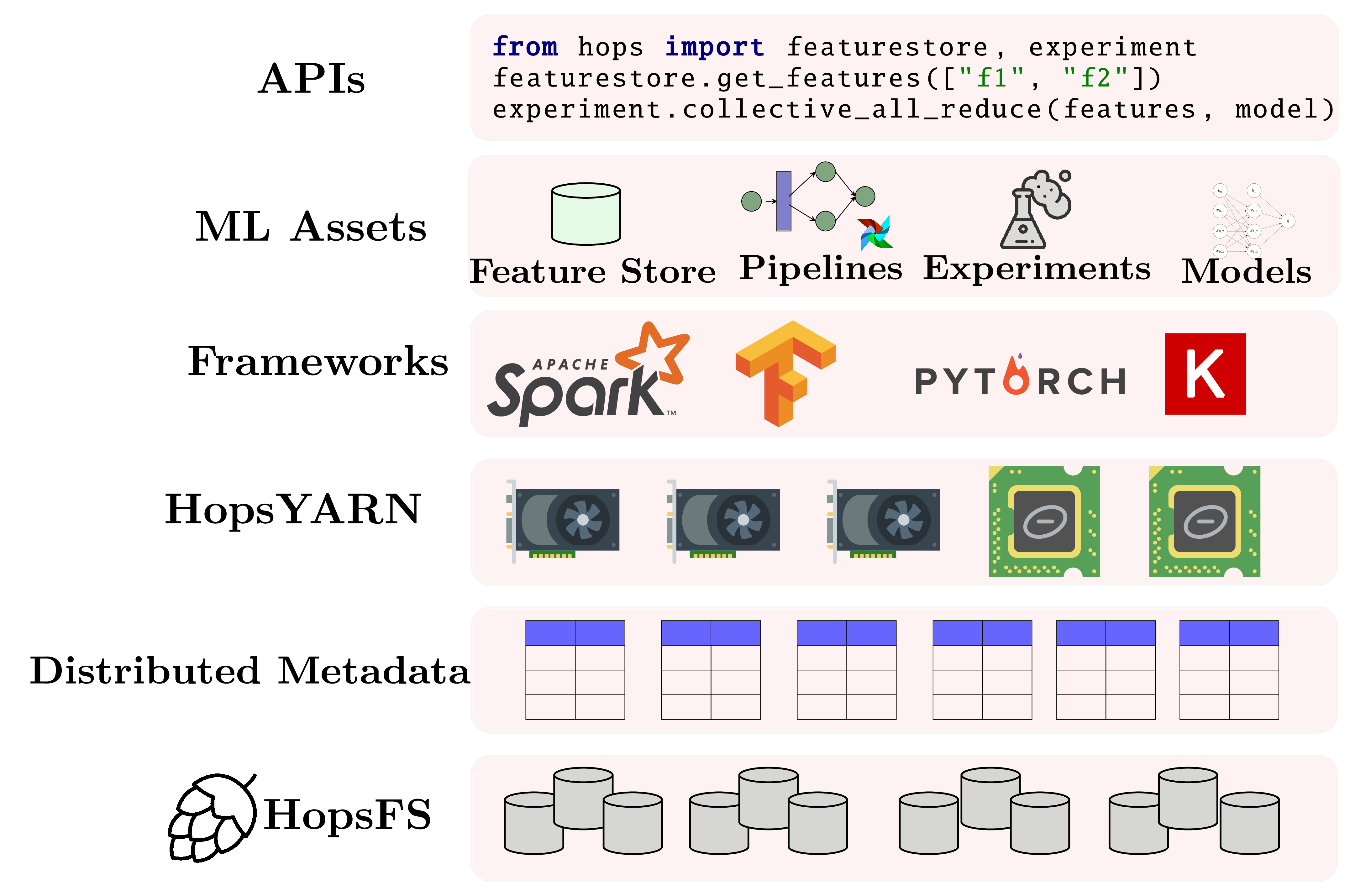
Hops-util-py; Hops-util-py is a python library for deep learning and data processing. Code repository
FastTextOnSpark; FastTextOnSpark is an implementation of the FastText algorithm for training word embeddings that runs on Spark, the first distributed implementation in the world. Code repository 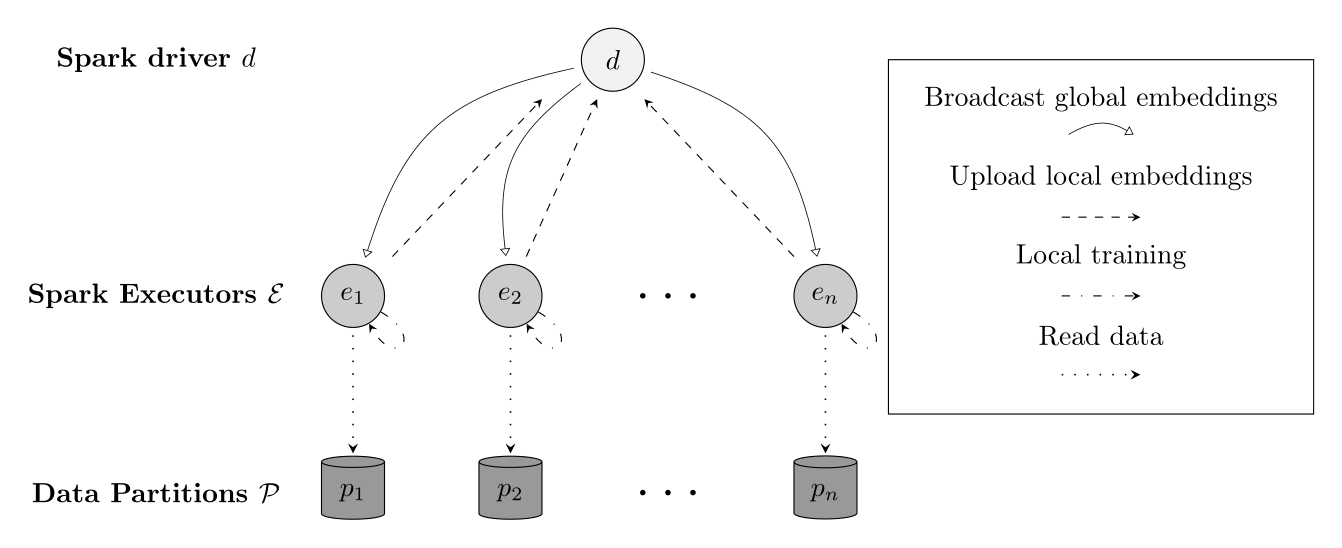
MLFD; Implementation of a next-generation failure detector for distributed systems with provable strong completeness, using a machine learning model updated with streaming data to detect machine failures. Code repository report
FashionRec; Implementation in Tensorflow of a multi-class multi-label text classification model using probabilistic labels learned from weak supervision and support for pre-trained word embeddings. repo
Erlang Pengine; Erlang Pengine is a distributed erlang client to a prolog pengine server. It enables you to run first-order logic programs and constraint programming programs from Erlang. Code repository 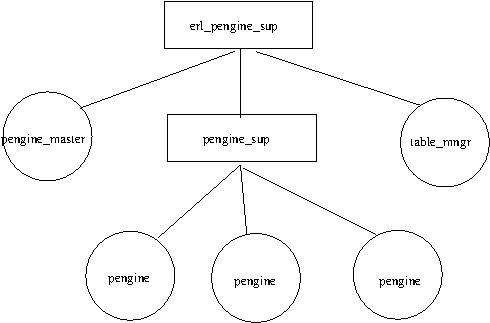
Distributed Linearizable Key-Value Store; Implementation of a provable linearizable key-value store using virtually synchronous group communication and passive replication. Code repository report
Logoot-Undo4J; Java implementation of CRDT for Logoot-Undo: Distributed Collaborative Editing System on P2P networks. Code repository report
SSL VPN; A C implementation of a SSL VPN that supports secure key exchange and encrypted communication. Code repository
SemWebTutorial; Semantic Web Tutorial. Code repository; Report
Advent Of Code 2016 in Prolog; Implementation of the Advent of Code series of challenges year 2016 in Prolog. Code repository
DataMining; Implementation of various data mining algorithms. Code repository; Report
AgentProgramming; Programing of Multi-Agent Systems Code repository; Report 1; Report 2